Watchlist Management
Sanctions screening systems depend on reliable watchlist data. Financial institutions screen customers, counterparties, and transactions against regulatory lists published by governments and international bodies. Before screening can occur, these lists must first be ingested into the organisation's compliance infrastructure.
Watchlist ingestion refers to the process of collecting sanctions lists from authoritative sources, importing them into a central system, and preparing them for use by screening engines. While this step often receives less attention than screening algorithms or investigation workflows, it forms the foundation of an effective compliance programme.
Poor ingestion processes can introduce data inconsistencies, delays in list updates, and duplicate records that weaken the accuracy of sanctions screening. By contrast, well designed ingestion pipelines ensure that screening systems always operate on reliable and up to date regulatory data.
This guide explains how watchlist ingestion works, the operational challenges organisations encounter, and the best practices that help compliance teams maintain high quality sanctions data.
Why Watchlist Ingestion Matters
Sanctions lists are published by multiple authorities around the world, each using different formats and update mechanisms. Some regulators release structured data feeds, while others publish list updates through documents or web updates.
For example, institutions frequently rely on regulatory sources such as the UK financial sanctions consolidated list and the OFAC Specially Designated Nationals list data formats when building their sanctions screening controls.
Because these lists originate from different jurisdictions and follow different data models, organisations must standardise them before screening systems can evaluate the information reliably.
If ingestion processes are unreliable or delayed, screening systems may operate on outdated data, potentially exposing institutions to regulatory risk.
Where Watchlist Ingestion Fits In The Screening Pipeline
Watchlist ingestion occurs at the very beginning of the sanctions screening lifecycle.
Data Collection
Regulatory lists are collected from government sanctions authorities and other relevant sources.
Data Transformation
Raw data is transformed into structured schemas so that screening systems can interpret the information consistently. Many institutions perform this process through a structured watchlist management platform that consolidates sanctions feeds and prepares them for screening.
Screening Evaluation
Once the data is ingested and structured, screening engines compare internal customer or transaction data against the watchlist records. Systems such as modern customer screening solutions rely on these structured datasets when performing similarity matching.
Alert Investigation
When potential matches are detected, investigators review alerts using structured alert adjudication workflows that allow analysts to examine identifying attributes and document investigation outcomes.
Each of these stages depends on reliable ingestion of sanctions data.
Common Challenges In Watchlist Ingestion
Organisations frequently encounter operational challenges when ingesting sanctions lists.
Inconsistent Data Formats
Different regulators publish sanctions data using varying formats and structures. This inconsistency makes it difficult to integrate lists into screening systems without transformation.
Delayed Updates
Manual ingestion processes may introduce delays between the publication of sanctions updates and their availability in screening systems.
Duplicate Records
The same sanctioned individual may appear across multiple regulatory lists with slightly different identifiers.
Unstructured Alias Data
Aliases may appear as free text fields rather than structured attributes, making it harder for screening engines to interpret them correctly.
Addressing these issues is essential for maintaining reliable sanctions controls.
Key Best Practices For Watchlist Ingestion
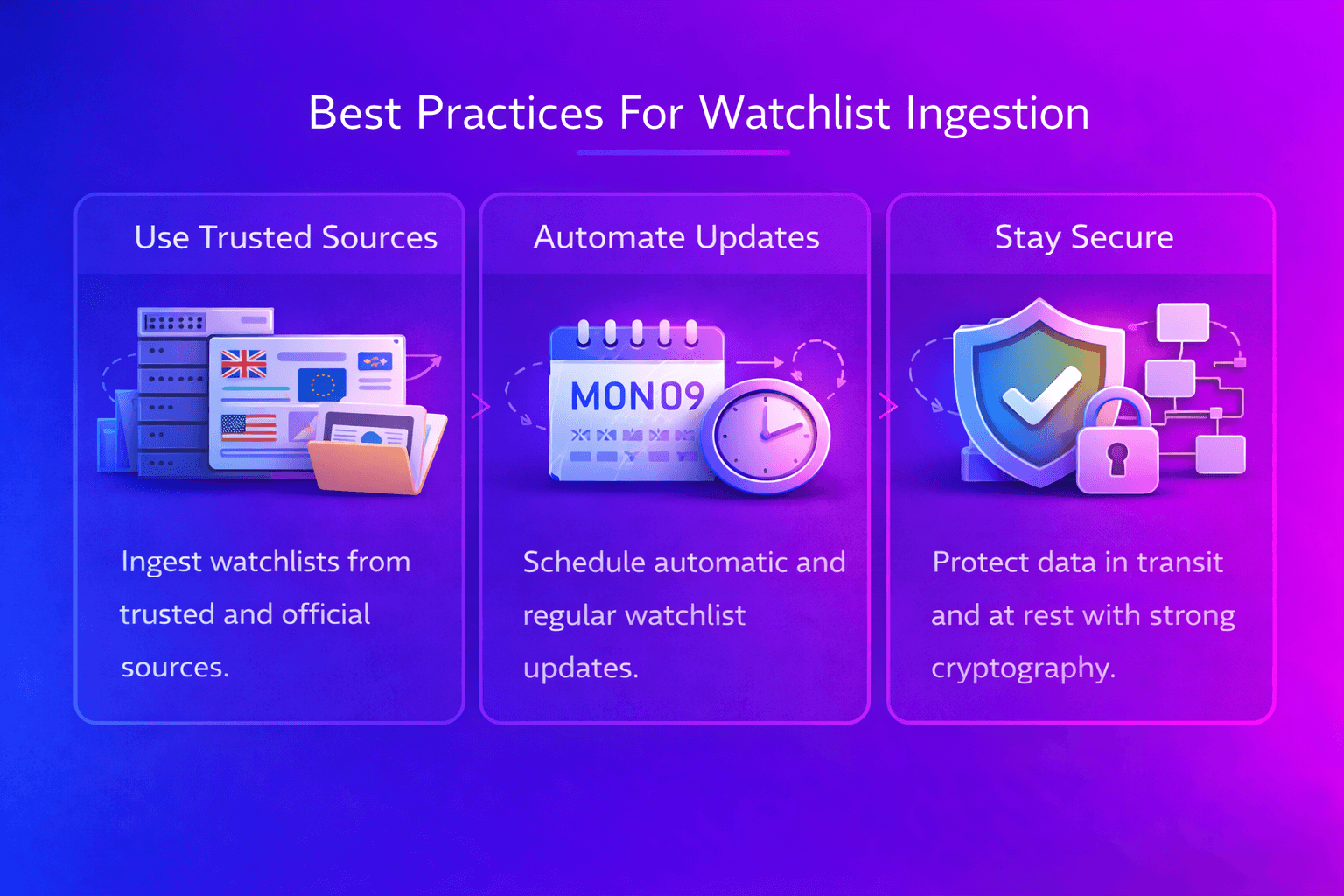
Organisations with mature sanctions screening programmes typically implement several ingestion best practices.
Automated Data Pipelines
Automated ingestion pipelines ensure that sanctions updates are processed quickly and consistently without manual intervention.
Source Verification
Institutions should confirm that sanctions lists originate from authoritative regulatory sources and are updated regularly.
Data Normalisation
Normalisation processes standardise field formats across lists so screening systems can compare attributes consistently.
Deduplication Controls
Duplicate records across multiple lists should be detected and consolidated to prevent redundant alerts.
Version Tracking
Maintaining historical versions of watchlists allows institutions to track regulatory changes and support delta screening strategies.
Together, these practices strengthen the reliability of screening infrastructure.
How Effective Ingestion Improves Screening Performance
Reliable ingestion pipelines directly improve the performance of sanctions screening systems.
When watchlists are ingested quickly and consistently, screening engines always operate on the latest regulatory information. Structured data also allows matching algorithms to evaluate multiple attributes rather than relying solely on name similarity.
As a result, investigators receive alerts that are more relevant and easier to assess. Compliance teams can therefore focus on genuine risk cases rather than operational noise.
What Strong Watchlist Ingestion Looks Like
Organisations with well designed ingestion frameworks typically demonstrate several characteristics.
Centralised Governance
A central system manages sanctions list ingestion and distribution to screening engines.
Consistent Data Models
Watchlist records follow consistent schemas that allow screening systems to interpret attributes reliably.
Rapid Update Processing
Sanctions updates from regulators are processed quickly so screening systems remain aligned with regulatory changes.
Integration With Screening Systems
Ingested data flows directly into screening engines without manual transformation.
These characteristics help maintain reliable sanctions monitoring programmes.
Professional Insight And Operational Confidence
Effective sanctions screening begins long before a screening engine evaluates customer data. In practice, the reliability of screening outcomes depends heavily on how watchlist data is collected, processed, and maintained. Even advanced matching algorithms cannot compensate for inconsistent or outdated sanctions lists.
Organisations that invest in structured ingestion pipelines, automated updates, and strong data governance gain greater confidence that their screening systems are operating on accurate regulatory information.
Practical Experience
Compliance practitioners often observe significant improvements in screening performance after strengthening ingestion processes.
Technical And Regulatory Expertise
Reliable ingestion requires both technical data engineering capabilities and regulatory awareness of sanctions obligations.
Building Confidence In Controls
When sanctions lists are ingested consistently and updated promptly, organisations can demonstrate that their screening controls rely on accurate and current regulatory data.
People First Compliance Content
Financial crime compliance ultimately depends on investigators and analysts who review alerts and assess potential risks. Technology assists by identifying potential matches, but the effectiveness of those alerts depends on the quality of the data entering the screening system.
Educational resources like this aim to help compliance professionals understand how foundational processes such as watchlist ingestion influence the reliability of financial crime controls.
Next Steps For Your Organisation
Many organisations discover during internal reviews that improvements in watchlist ingestion significantly strengthen the reliability of their sanctions screening framework.
If your organisation is evaluating its sanctions data pipelines or screening architecture, explore how your ingestion processes compare with current industry practices.





